A significant challenge organizations face is the ability to secure and protect information, both in transit and while at rest. In respect to securing information within email, we have two primary options available to us – S/MIME and Office Message Encryption (OME).
In this article we are going to look at how to leverage either of these options within Outlook on the Web. However, prior to looking at this, let’s quickly discuss a point of divergence between these two technologies.
A Quick Discussion of a Key Difference
First, both provide organizations with the ability to encrypt and protect information within emails. However, how they do this is very different. S/MIME uses a Public Key Infrastructure (PKI) which OME is underpinned by Azure Rights Management. This fundamentally changes the method in which the data is protected. While S/MIME uses a sender/recipient certificate model, OME leverages an encryption key assigned to the Exchange Online tenant. As a result, recipients of OME protected messages are required to perform authentication against the sending user’s tenant, as Azure Rights Management is what controls access to the information. In turn, if organizations which implement conditional access policies prohibiting external users from authenticating against the tenant, the recipient will be unable to open the content of the message. S/MIME differs in this, as the recipient’s public/private key pair allows them to open the content without further authentication.
Now, this does not mean that external recipients must have an account within the tenant. Rather, its just that the organization must make the decision to either deny or allow external accounts to authenticate for access to the content of the message. While this is beyond the scope of this document, I wanted to point it out so that if you are testing this solution within your organization, you are aware of this fact to assist you in your adoption of OME.
Secure/Multipurpose Internet Mail Extensions (S/MIME)
S/MIME is a technology which allows mail users to Sign or Encrypt messages. It uses a Public/Private Key Infrastructure to facilitate this.
To utilize S/MIME within the Outlook on the Web (OWA) client, perform the following steps:
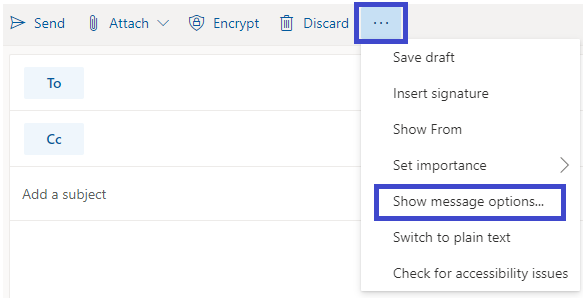
- At the New Message window, select the ellipsis icon, then select Show message options…
- At the Message Options window, select the Encrypt this message (S/MIME) checkbox, then select the OK button.
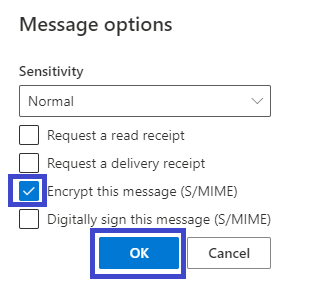
- This will encrypt the message to all the recipients of the message. This option does not require the use of a One-Time passcode or a login to the Sender’s M365 Tenant – that is, the message is protected utilizing the sender’s certificate. These are key differences between S/MIME and OME.
S/MIME Considerations
S/MIME requires the installation of a plug-in. Upon successful installation, the plug-in will be seen to the right of the address bar.

If the plug-in is selected, the user may select Microsoft S/MIME Options.

Of note, if the plug-in is not installed, users will not have the option to leverage S/MIME encryption.
Office Message Encryption (OME)
OME is a technology which allows mail users to restrict access to message contents. This is accomplished using rights management within the sender’s M365 tenant. OME differs from S/MIME in that OME does not leverage an organization’s established PKI. Furthermore, it is capable of leveraging One-Time passcodes or trusted organization logins to restrict access to the protected information.
A major consideration for the use of OME is establishing the proper framework and governance associated with the organization’s records management and data protection requirements.
To utilize OME message protection out of the box within the Outlook on the Web (OWA) client, perform the following steps:
- At the New Message window, select the Encrypt button. Once encryption has been applied, the options to change permissions and remove encryption will appear.
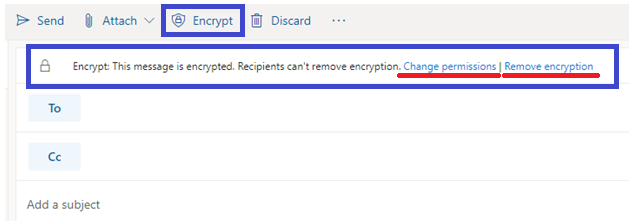
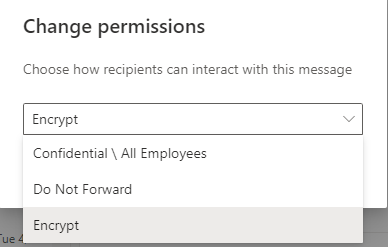
- If the user selects change permissions, the following window will appear:
Note: It is recommended that prior to adopting OME, organizations carefully plan out the use case scenarios in which the mission’s objectives will be served. For DoD and Federal agencies, this should include the organization’s stakeholders who are responsible for data classification, records management, and compliance with NIST standards.